Real-time Anomaly Detection and Alerting Systems
Real-time Data Ingestion and Preprocessing
Modern financial systems generate massive volumes of data in real-time, encompassing various sources like transaction logs, market data feeds, and internal operational metrics. Efficiently ingesting and preprocessing this data is crucial for anomaly detection. This involves transforming raw data into a format suitable for analysis, handling missing values, and normalizing data points to ensure consistency and accuracy. Robust data pipelines are essential to support high-throughput data ingestion, enabling rapid detection of anomalies as they occur.
Key aspects of this preprocessing stage include data cleaning, which involves handling outliers and inconsistencies, and feature engineering, which creates new features from existing ones to enhance the model's ability to identify anomalies. Failure to properly manage data quality at this stage can significantly impact the accuracy and reliability of the anomaly detection system.
Anomaly Detection Algorithms
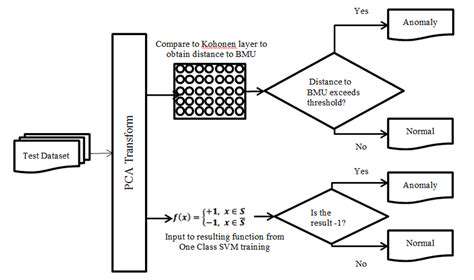
A variety of algorithms are employed for real-time anomaly detection, each with its strengths and weaknesses. Machine learning techniques, such as Support Vector Machines (SVMs) and clustering algorithms like K-Means, are frequently used. These algorithms learn patterns from historical data and flag deviations from these patterns as anomalies. Choosing the right algorithm depends on the specific characteristics of the data and the desired level of accuracy.
Deep learning models, particularly neural networks, are increasingly popular due to their ability to learn complex, non-linear relationships in data. These models excel at identifying subtle patterns and anomalies that traditional methods might miss. However, the training and deployment of deep learning models can be computationally intensive.
Alerting Mechanisms and Notifications
An effective anomaly detection system must have robust alerting mechanisms to immediately notify relevant personnel about potential issues. Different types of alerts can be configured, such as email notifications, SMS messages, or in-app alerts, tailored to the urgency and severity of the detected anomaly. Prioritizing alerts based on predefined thresholds and risk levels ensures that critical issues receive prompt attention.
These notifications should be accompanied by comprehensive information regarding the detected anomaly, including the specific data points involved, the time of occurrence, and potentially a prediction of the potential impact. This level of detail empowers the users to respond swiftly and effectively to the detected anomalies.
Integration with Existing Systems
Successful anomaly detection requires seamless integration with existing financial systems. This integration allows for the efficient flow of data between the detection system and other applications, such as trading platforms, risk management systems, and compliance tools. The system should be able to identify anomalies in real-time, and deliver the information to the appropriate parties within the organization.
Integration also encompasses the ability to adapt to evolving data structures and changing business requirements within the financial ecosystem. Flexibility and adaptability are essential to ensure the system remains relevant and effective in the face of ongoing changes in financial market conditions and regulatory environments.
Scalability and Performance
Real-time anomaly detection systems must be designed for scalability to handle increasing volumes of data and diverse data sources. This involves using distributed computing frameworks and optimized algorithms to process data efficiently. Performance is critical, as delays in detecting anomalies can lead to significant financial losses or operational disruptions.
The system should be able to manage fluctuating data volumes and maintain high accuracy with minimal latency, even during peak periods of market activity or high-volume transactions. Robust infrastructure and well-designed algorithms are crucial for ensuring timely and reliable anomaly detection in a high-pressure environment.
Security and Privacy Considerations
Protecting sensitive financial data is paramount in anomaly detection systems. Robust security measures, including encryption and access controls, are essential to prevent unauthorized access and data breaches. Compliance with relevant regulations, such as GDPR and CCPA, is mandatory.
Privacy considerations also play a critical role, ensuring that only necessary data is collected and utilized for anomaly detection. Careful consideration of data anonymization techniques and compliance with privacy regulations is crucial to maintain trust and build a robust, ethical system.